OT Cybersecurity & Intrusion Detection
Unified Platform for DER Security
Cybersecurity, aggregation, and validation in a single architecture.
Deploy where you need it: cloud, on-premise, or edge.
<1s
Detection Latency
93%
Fewer False Positives
50+
DER Device Types
Zero
Agents Required
The Challenge
Traditional IT & OT Security Is Blind to DER Threats
Firewalls and SIEM tools can’t inspect DER protocols like IEEE 2030.5, SunSpec Modbus, OCPP and others. They don’t understand power system physics. An attacker manipulating your grid looks like normal traffic.
IT Security Tools
Monitor network traffic, file hashes, IP reputation. Cannot inspect DER protocol payloads. Blind to commands that are syntactically valid but operationally dangerous.
Generic OT/ICS Security
Built for SCADA/PLC environments. Not designed for distributed DER fleets. Require agents on each device – impractical for 10,000+ inverters and energy assets connected to the grid.
DERSec Sentry
Purpose-built for DER OT security. Behavioral analysis of power telemetry, protocol-aware deep packet inspection, and physics-based anomaly detection. Zero agents. Sub-second detection.
PLATFORM CAPABILITIES
Platform Features
Purpose-built cyber-physical security for inverter-dominated grids, AI data centers, microgrids, and distributed energy fleets.
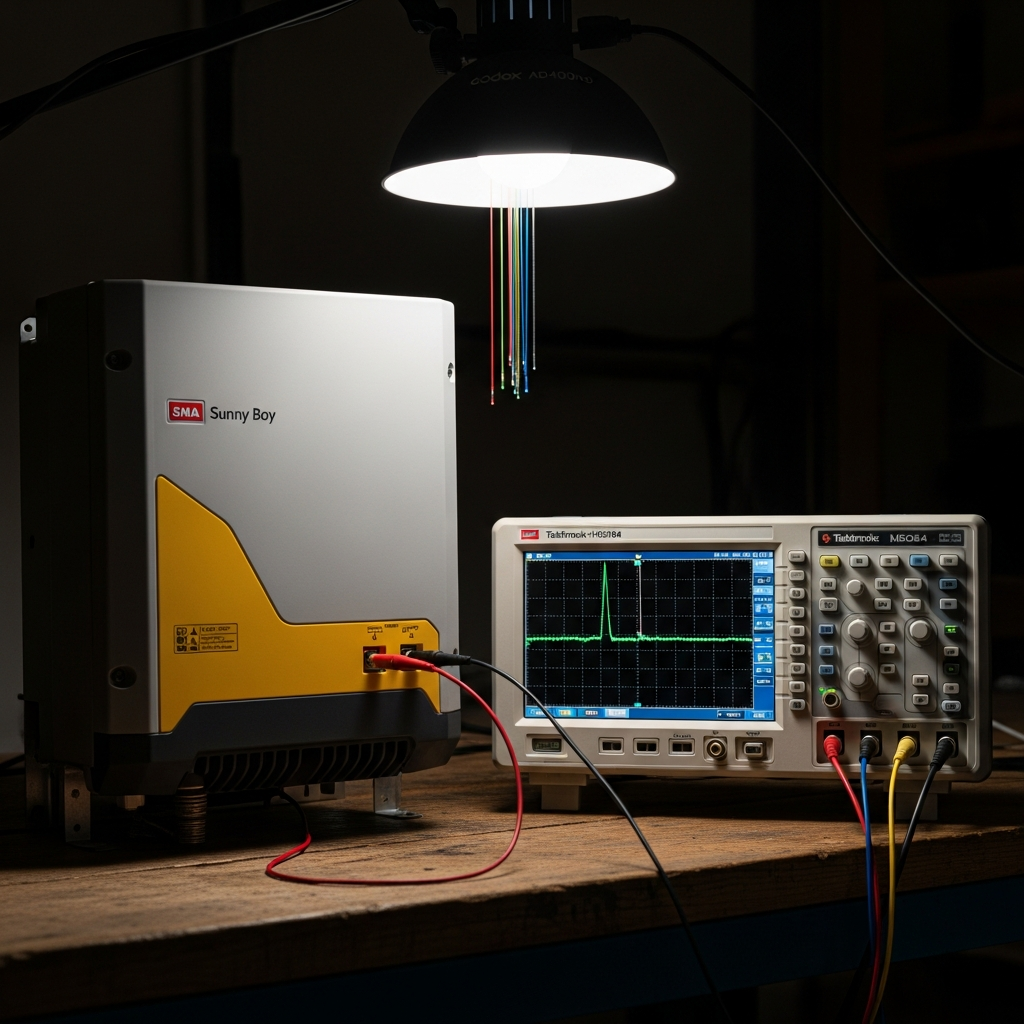
Cyber-Physical Intrusion Detection
Physics-informed threat detection that validates protocol commands against real power system behavior. Identifies malicious voltage, frequency, and active power manipulation invisible to network-only tools.
Explore Sentry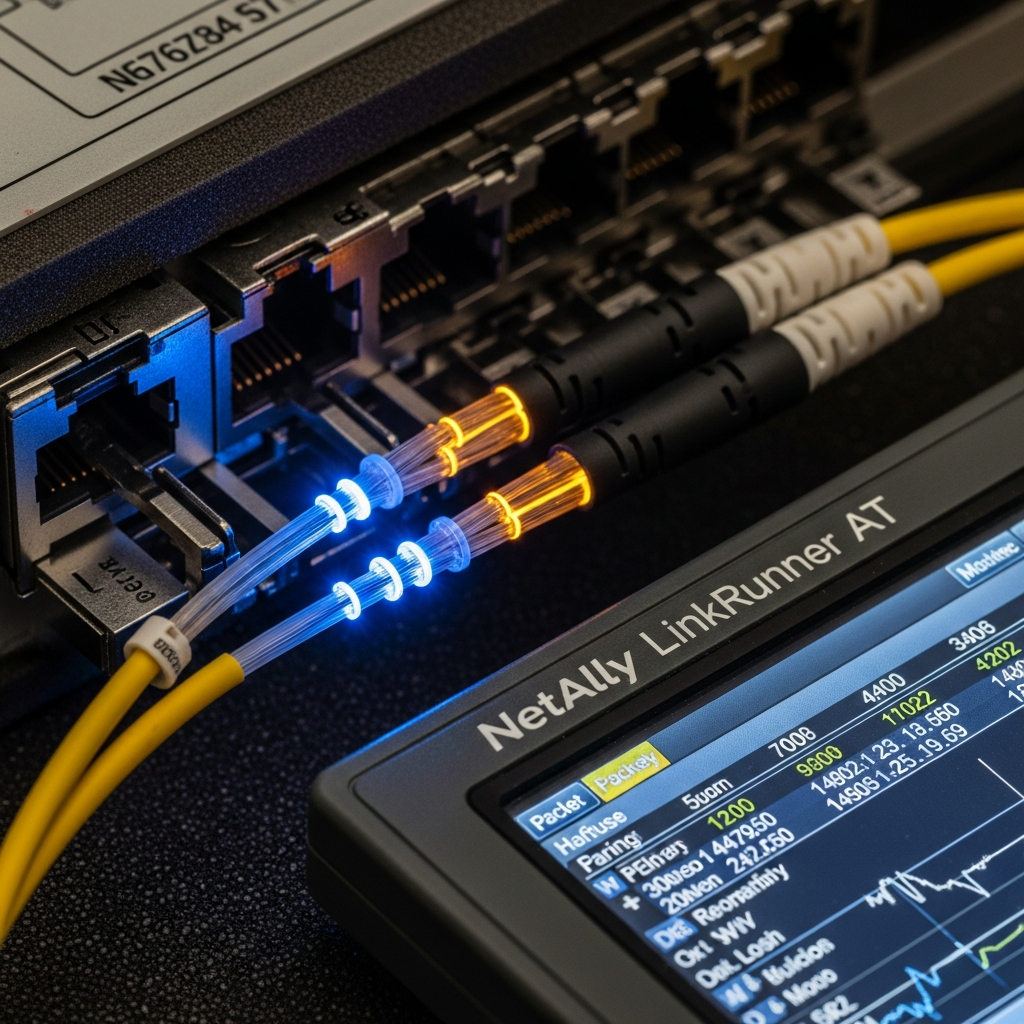
Protocol-Native Security
Deep packet inspection and deterministic validation across IEEE 2030.5, SunSpec Modbus, DNP3, OCPP, and OPC-UA—securing the control plane that moves power.
See Protocols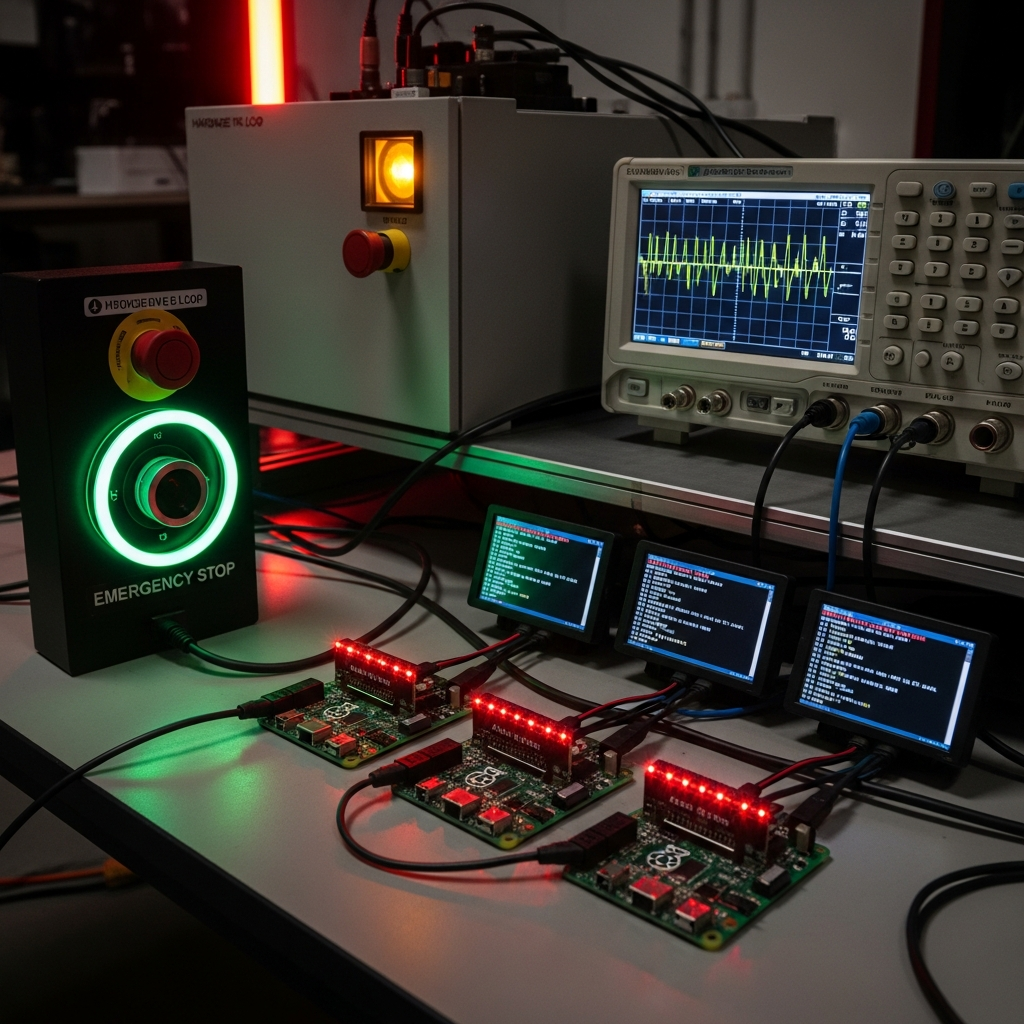
Digital Twin Intelligence
Grid-aware digital twins for behavior modeling, impact estimation, and proactive threat hunting. Simulate real-world grid response before attacks manifest.
Explore DERSim
Secure DER Aggregation
Standards-native IEEE 2030.5 aggregation and orchestration for massive DER fleets, VPPs, and grid-edge resources—with built-in PKI, encryption, and anomaly detection.
Explore DERSync
Edge AI & Physics Validation
Sub-second protocol inspection, ML inference on process variables, and physics-based command enforcement deployed at substations, microgrids, and remote DER sites.
See Architecture
Fleet Visibility & Risk Posture
Unified system of record for asset posture, protocol behavior, physics validation, and fleet-wide cyber risk—integrated into SOC and grid operations workflows.
See DashboardWhat We Detect
Threats, Drift, and Anomalies
Our AI engine uses neural networks and GANs to continuously improve detection accuracy, reduce false positives, and identify both cyber threats and configuration issues.
Cyber Threat Detection
Command injection, firmware tampering, protocol manipulation, unauthorized control sequences, man-in-the-middle attacks on DER communications, and coordinated fleet-level attacks.
Configuration Drift
Detect when device settings deviate from approved configurations — frequency-watt curves, voltage ride-through parameters, power limits, and communication certificates that have expired or been modified.
Operational Anomalies
Identify performance degradation, failing components, firmware bugs, and interoperability issues before they become security incidents. Correlate anomalies across the fleet to detect systemic issues.
WHY DERSEC
Built Different.
Built For DER.
Agentless
Zero footprint on devices
Passive monitoring through network taps. No agents, no firmware dependencies, no expanded attack surface.
Protocol-Native
Semantic-level DPI
Understands SunSpec Modbus registers, IEEE 2030.5 function sets, DNP3 objects, OCPP structures—not just packets.
Continuously Learning
AI that adapts to your fleet
Adapts to seasonal patterns, firmware changes, fleet growth. No manual rule tuning. Accuracy compounds.
Fleet-Scale
Correlated detection
Spots coordinated attacks across thousands of devices—the kind invisible when monitoring assets individually.
Compliance-Ready
Audit-ready from day one
Auto-generates evidence for NERC CIP, IEEE 2030.5, Rule 21, and emerging DER mandates. Full chain of custody.
SOC-Integrated
Works with your stack
Splunk, Sentinel, QRadar, SOAR playbooks, CEF/STIX/TAXII—enriched with DER-specific context.
See DERSec in Action
Request a live demo to see how DERSec detects threats across your DER fleet in real-time.